12 Computer Security Mistakes You're Probably Making
Here are 12 common mistakes that result in malware infections, computer viruses or getting your computer outright hacked.


If you were a hacker looking to release some new phishing scam, virus, or botnet control scheme, what would be the profile of your ideal victim? What bad habits would they have that you could easily exploit?
Here are some definite bad habits that will have your machine infected six ways to Sunday in no time.
Avoiding Updates
A sure-fire way to leave a machine vulnerable is to avoid updating your system, software, and security.
Windows Update, and Automatic Updates for Java, Flash, PDF Reader, Quicktime, Office, and other pieces of software frequently provide regular security updates as leaks are discovered. While it's true that some updates introduce new security vulnerabilities, for the most part, it's safer to update, rather than not.
Even if a machine is armed with the latest and best antivirus software, having automatic updates disabled is akin to leaving the gates to your fortress unbarred and unguarded.
Keeping Old Versions of Applications
Related to number one, another possible vulnerability is keeping old versions of a program. Even if you're already running the latest Java, Flash, or PDF Reader, don't forget that some older versions do not automatically update or remove themselves when a new version is installed. As with un-updated software, keeping an old version in your system along with a new one can serve as a gateway that a malicious programmer can exploit.
Disabling User Account Control (UAC) Features
"User Account Control" alerts users when a program tries to make changes to your Windows settings, particularly things that require Administrator privileges. If left disabled, users get absolutely no warning when a program, whether beneficial or malicious, attempts to change the Windows system. Surely, a deliciously tempting vulnerability.
Sign up to get the BEST of Tom's Guide direct to your inbox.
Get instant access to breaking news, the hottest reviews, great deals and helpful tips.
Double-Clicking on Everything
There's always that user who, once taught to double-click, can't help but double-click everything. A file in an email? Double-click away! Music and videos with extension ".EXE"? It's great, quick, double-click! The file on the USB stick or Office carries a folder even though it is only an icon file? Double-click all the things!
Downloading Programs From Anywhere
Hasty Google searches combined with clicking on the first download link that shows up is another bad habit that's easy to exploit. A user that doesn't make sure that they're downloading a file from an official website or download mirror is another easy mark for spyware advertising embedded in a phony file, or 'downloaders' that cram machines with malware.
Piracy, Cracks and Keygens
Software piracy. An ancient and honorable computing tradition, isn't it? These days, a little patience and a decent web search will quickly give you dozens of cracked files and keygens so that you can enjoy your less-than-legal copies of Windows, Office, or Adobe Creative Suite. Surely it doesn't matter that over 90% of them (and frequently the host sites) are vectors of malware.
Shortlinks
The rise of social networks such as Facebook and Twitter has also increased the popularity of shortened URL services such as bit.ly, goo.gl, TinyURL and more. These are also perfect for concealing a link's true destination. If users don't have some sort of link preview add-on for their browser, it's a great vector to sucker people into jumping blindly into an exploit or phishing site.
Using Open, Unsecured Wi-Fi
Open up your Wi-Fi to everyone! It's the brotherly thing to do, isn't it? Open, unsecured networks, or those using the obsolete WEP encryption protocol are easy vectors, and even the newer WPA encryption is vulnerable if you use an easily guessed code. Another route, of course, is file sharing over Wi-Fi. (Editor’s Note: Here is a handy guide on how to secure your wireless router.)
Surfing on an Administrator-Enabled Account
Many types of malware and web exploits fail to run when using a "Standard" account rather than "Administrator" account (especially in combination with UAC controls). A careless user surfing the web with an administrator account can be a gold mine.
Continuing to Use Windows XP
Windows XP is a sieve! Even Microsoft seems to have conceded this point. The latest Microsoft Security Intelligence Report shows that almost 4% of XP machines (already running antivirus, the stats are much worse when you look at those without AV) are infected. This is compared to a measly 0.02% of Windows 8 64-bit machines. Two hundred times more likely to be infected due to numerous exploits and security leaks fixed in later Windows versions! What's more, with Microsoft's extended support for Windows XP eliminated as of April 2014, that's sure to rise.
Using the Same Password. Everywhere
Everywhere you go on the web, you'll need to login, sign up, register, and otherwise authenticate your ID. Lazy users stick to using a single password wherever they go, making it that much easier to find out their login details, and requiring only a single leak to break open all of their user accounts and logins. And, of course, you can compound that by making passwords easy to guess. Birth dates, middle names, short dictionary words, and common ones such as 'qwerty,' 'password,' and 'aaa'.
Not Using Antivirus Software
This one's a no-brainer. Real geeks don't use antivirus? Please. It's easy to take advantage of such manly bravado. Even safe, hyper-vigilant surfing habits will only take you so far, and even perfectly legitimate sites can be temporarily suborned to spread infections.
Unless you're intentionally leaving your system open for infections, do yourself a favor and install good antivirus software, such as any of the free or paid options reviewed below.

Still the best bang for the buck in antivirus software
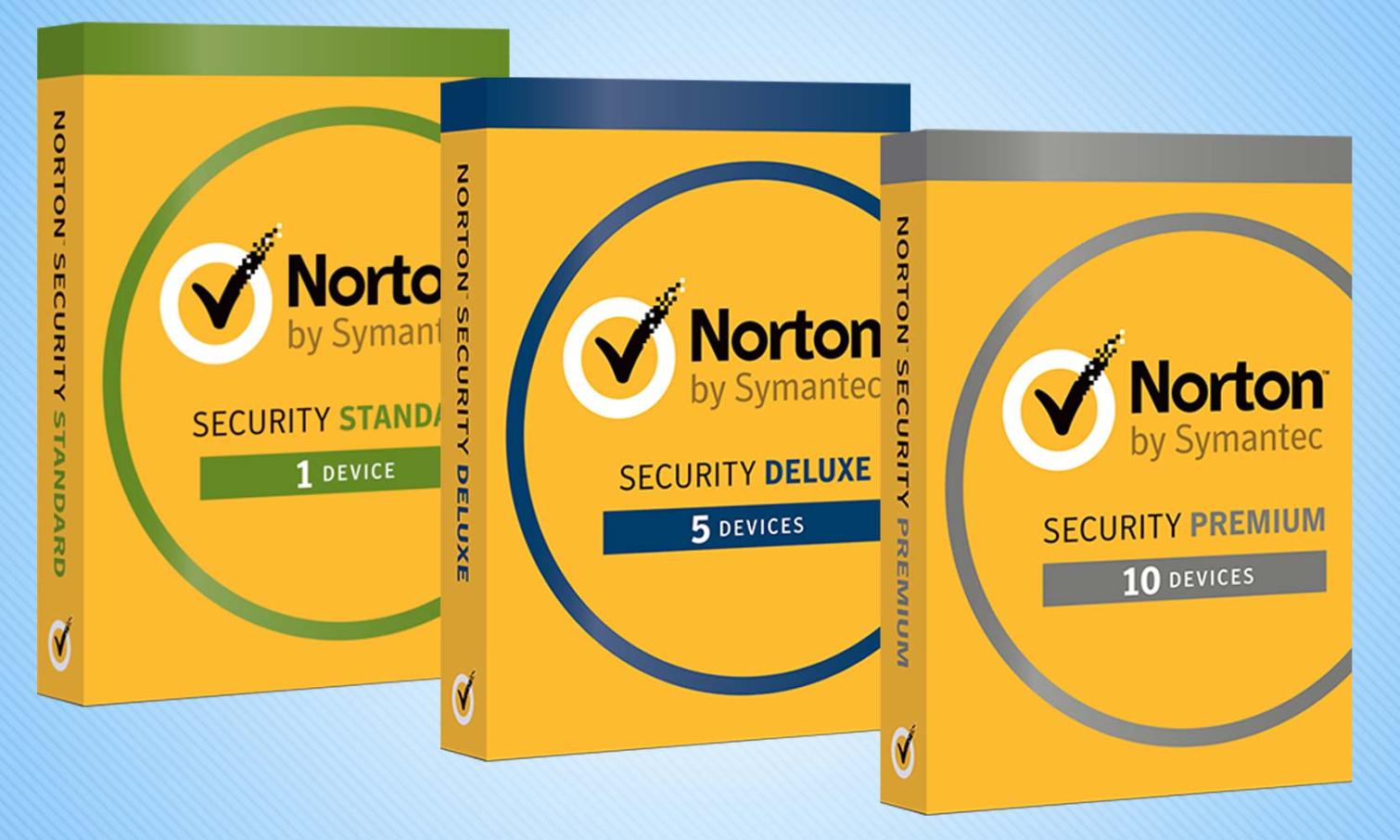
Norton's Windows antivirus products offer very good malware protection and extra privacy software, but lack some basic security features.
Related Security Guides:
Follow us @TomsGuide, on Facebook and on Google+.


